KringleCon | CURLing Master & AD Privilege Discovery | CTF Challenge Solution
Holly Evergreen: CURLing Master
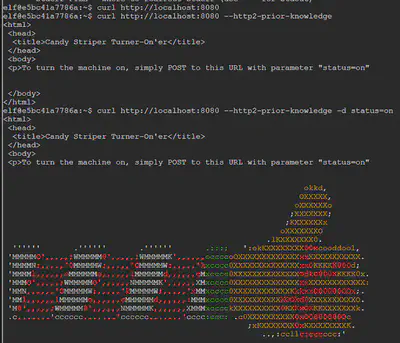
We know that the candy striper machine can be turned on by sending a request to port 8080 on localhost (127.0.0.1). But we do not know what request to send. To investigate further, we send a generic request for the URL localhost at port 8080. We weren’t able to get an intelligible response to this request. Recall that Holly Evergreen hinted at HTTP2. We use the --http2 option in curl to see if we can get an intelligible response. No good. So we try again with the --http2-prior-knowledge option and are able to get a readable response from the server. This response tells us that we simply need to make a POST request with the parameter status set to on.
We are able to get the candy stripper machine started after sending the required POST request in the following manner:
curl http://localhost:8080 --http2-prior-knowledge -d status=on
Question 5 AD Privilege Discovery
This challenge asks us to find a reliable path from a Kerberoastable user to the Domain Admins group. This is easy to do using the tool bloodhound. We are given an virtual machine image as part of the challenge with the tool and the relevant data already loaded on it. All we have to do is mount the image and utilize the bloodhound tool to locate the Kerberoastable users.

Bloodhound has preset queries, one of which is ‘shortest path to domain admins from Kerberoastable users. We use this query and are presented with the following path diagram that shows paths from Kerberoastable users to domain admins. After we eliminate any path that has RDP, the shortest path we get is from user LDUBEJ00320@AD.KRINGLECASTLE.COM
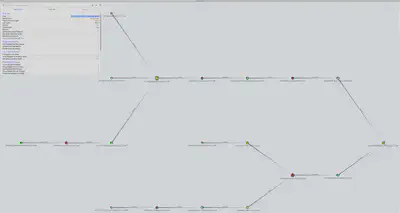
Answer: LDUBEJ00320@AD.KRINGLECASTLE.COM